Security
Finding LDAP Injection in …
Overview
Structured security code review is a practical and effective approach to finding real vulnerabilities. In this post I walk through how I applied a systematic review methodology to Snipe-IT, a popular open-source IT asset management platform, and how that approach led me directly to a …
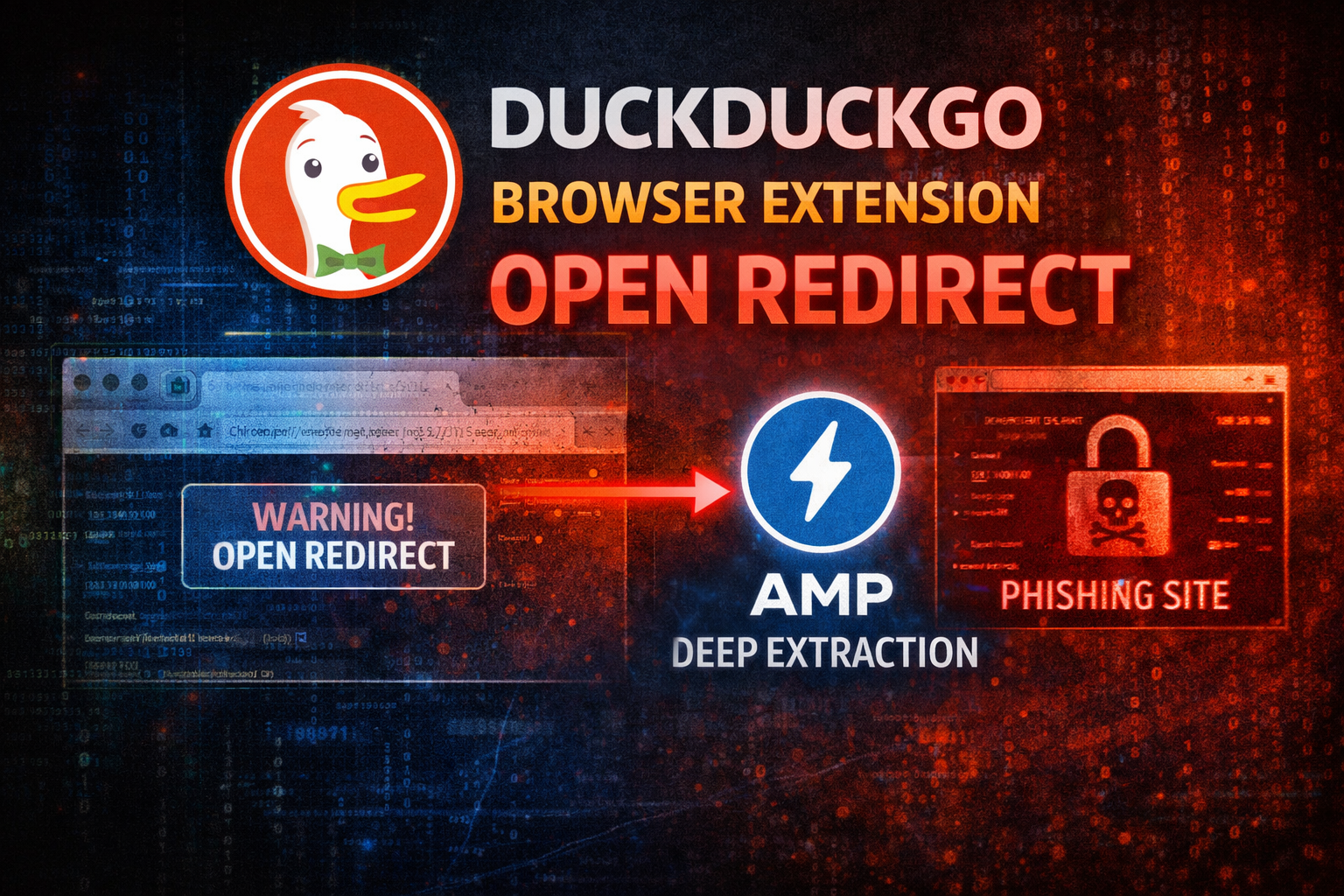
AMP Deep Extraction Open …
Background
I’ve been spending some time looking at browser extensions as a security target. They are interesting because they sit between the browser and the network, operate with elevated permissions, and users generally trust them implicitly. The whole point of a privacy extension is that …
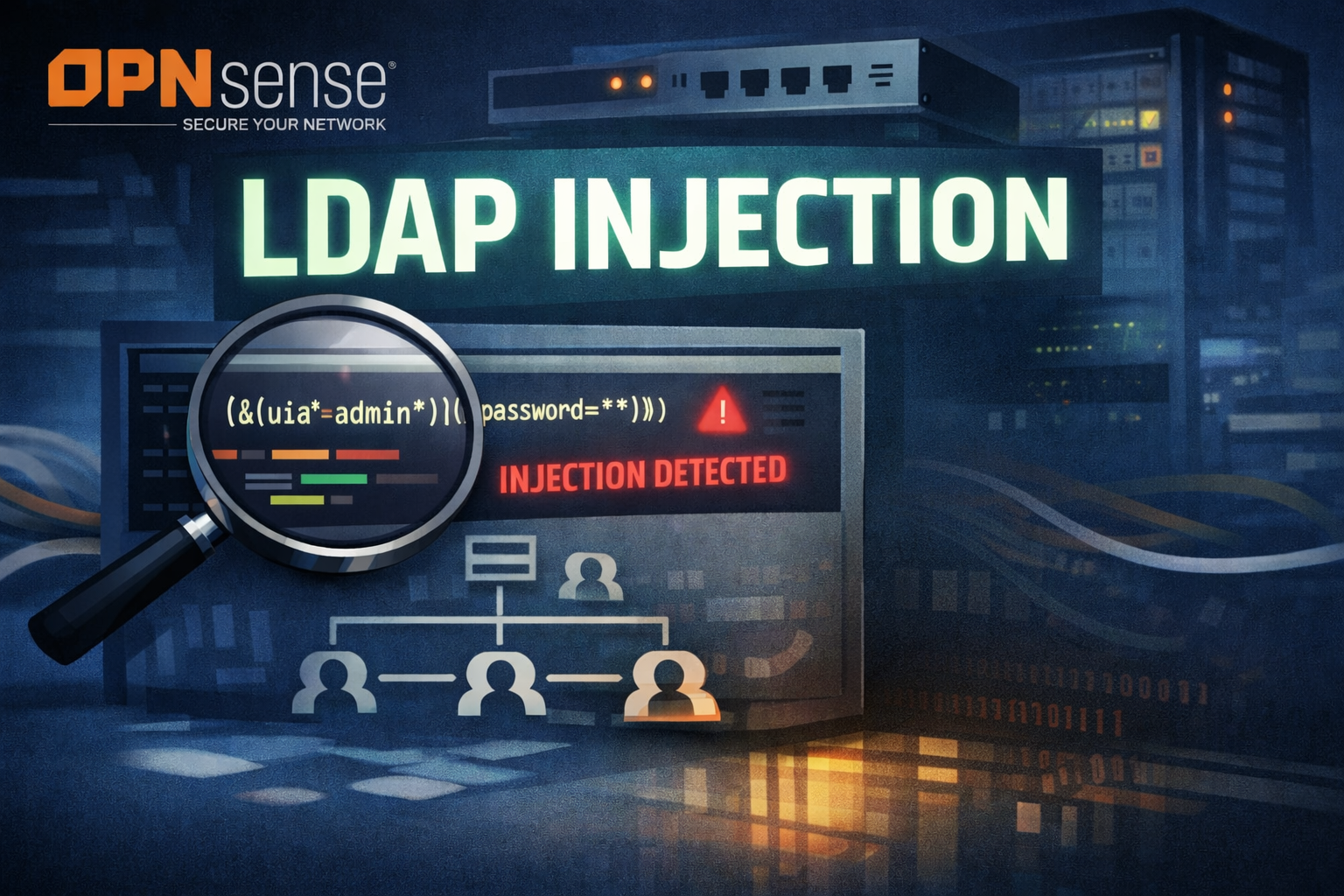
OPNsense: LDAP Injection …
OPNsense is a popular open-source firewall and routing platform built on FreeBSD. It handles network perimeter security for a huge range of environments, from home labs to enterprise edge routers, and it supports LDAP and Active Directory integration for centralized authentication. That makes the …
Finding a Svelte SSR XSS …
Background
I’ve been working through Vercel’s bug bounty program, which explicitly calls out server-side rendering and compiler security as focus areas. Svelte is a Tier 1 target in that program, and since Svelte 5 introduced a significant rework of how components are compiled and …
Finding an Authentication …
Background
I’ve been running Seerr at home for a while now. It’s a self-hosted media request manager, forked from Jellyseerr/Overseerr, and it’s the kind of app that gets exposed to the internet pretty regularly since family members need to be able to submit requests. That always …
CSS Injection in …
If you run a home lab or a self-hosted setup, there is a good chance you have come across dashdot. It is a slick, glassmorphism-style server monitoring dashboard that shows you CPU load, RAM usage, network stats, and more in real time. It also has a handy single-widget embed mode, where you can pull …